
XoloC2
Open-source Command & Control framework for authorized penetration testing.
|

Open-source Command & Control framework for authorized penetration testing.
|
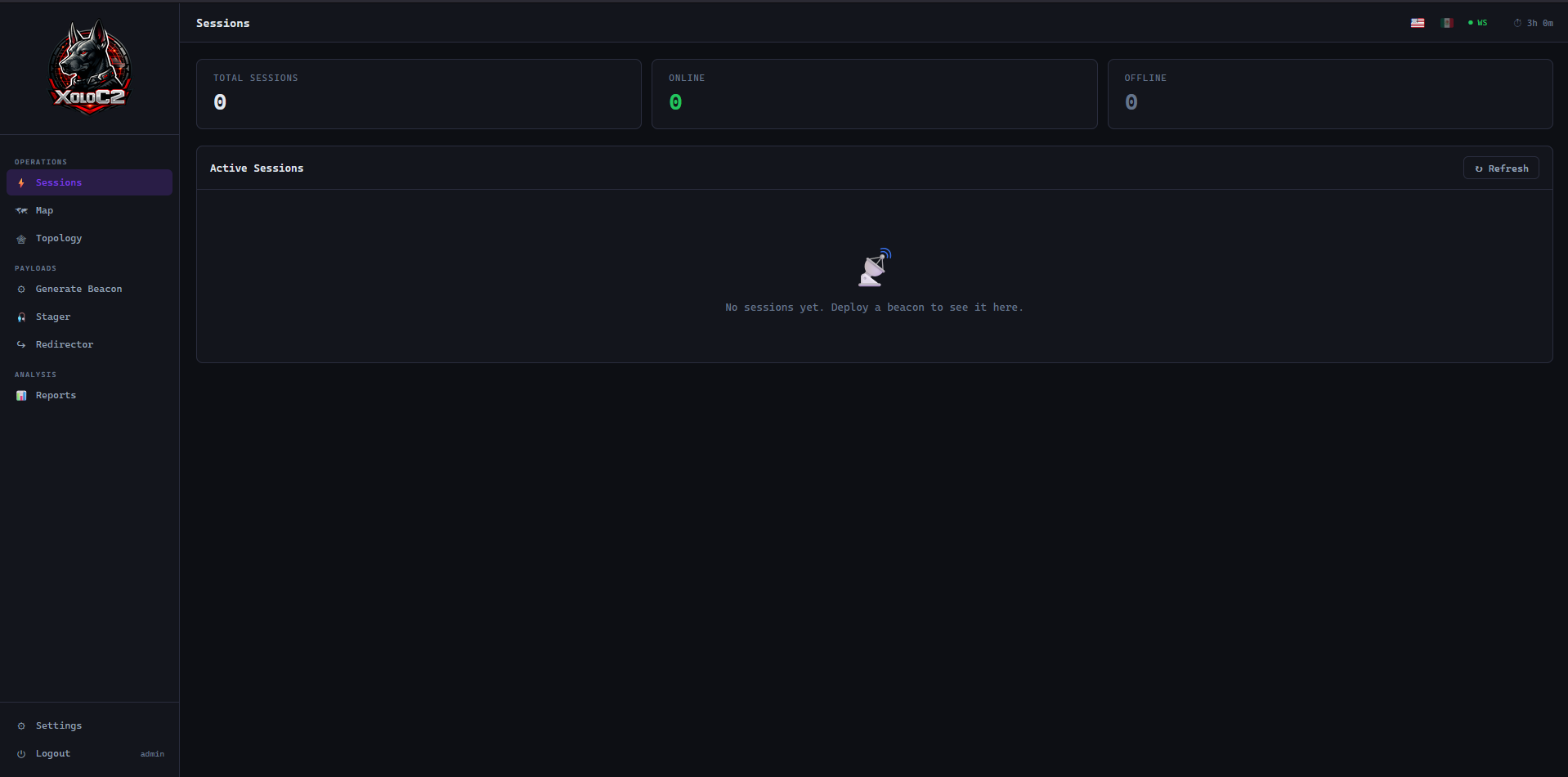
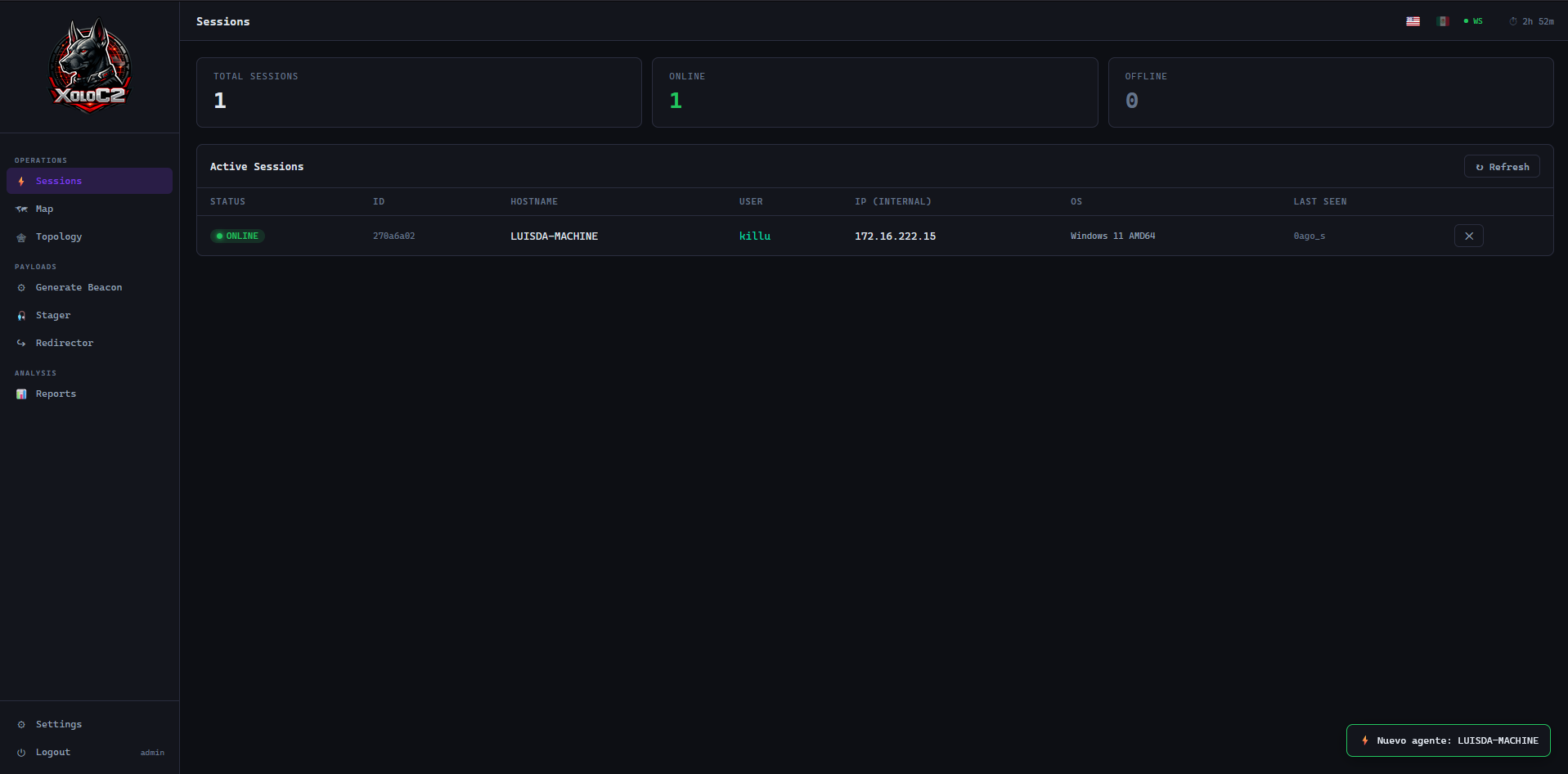
Sessions Dashboard
Terminal & File Browser
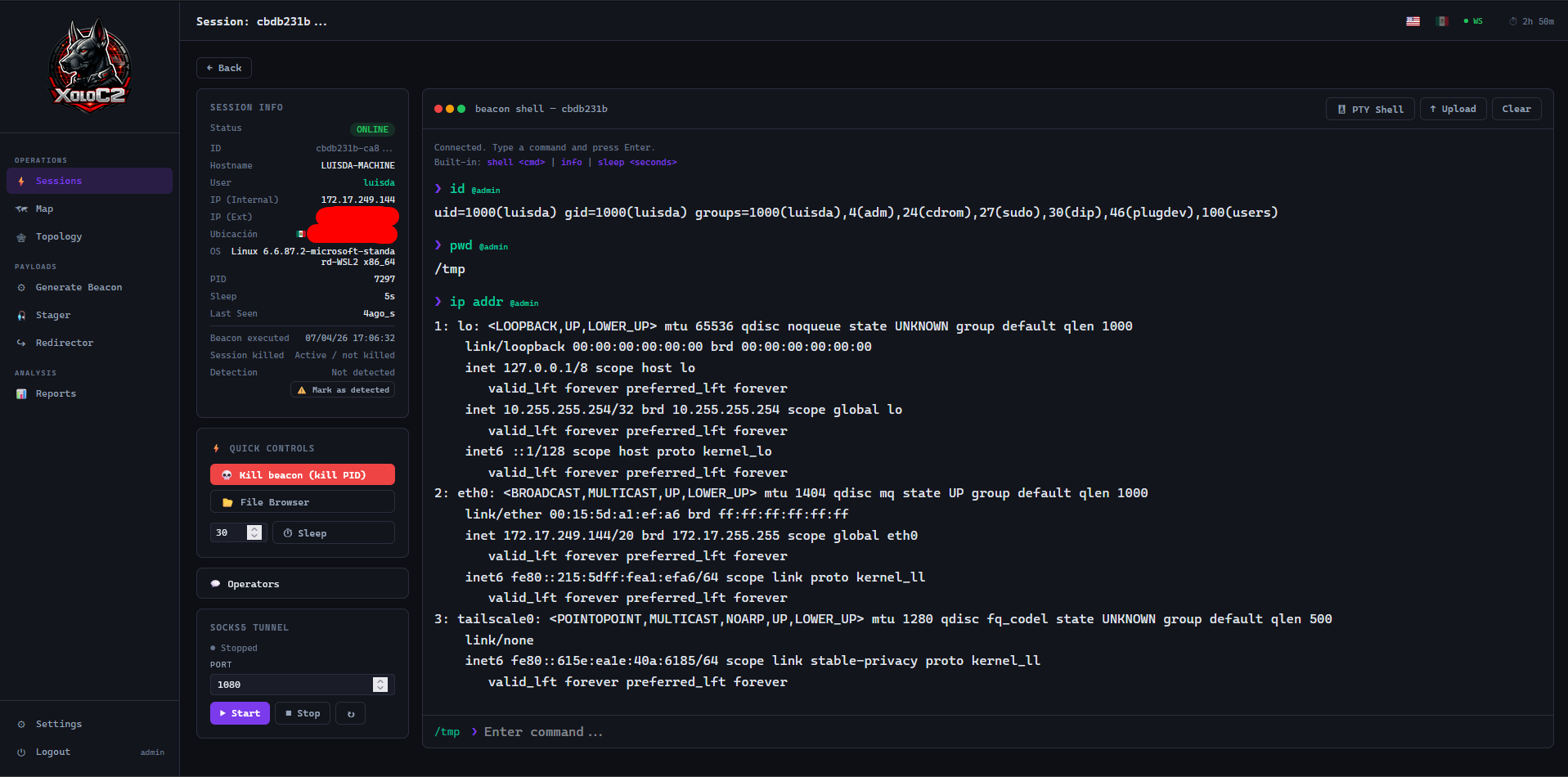
PTY Shell + SOCKS5 Tunnel
Beacon Generator
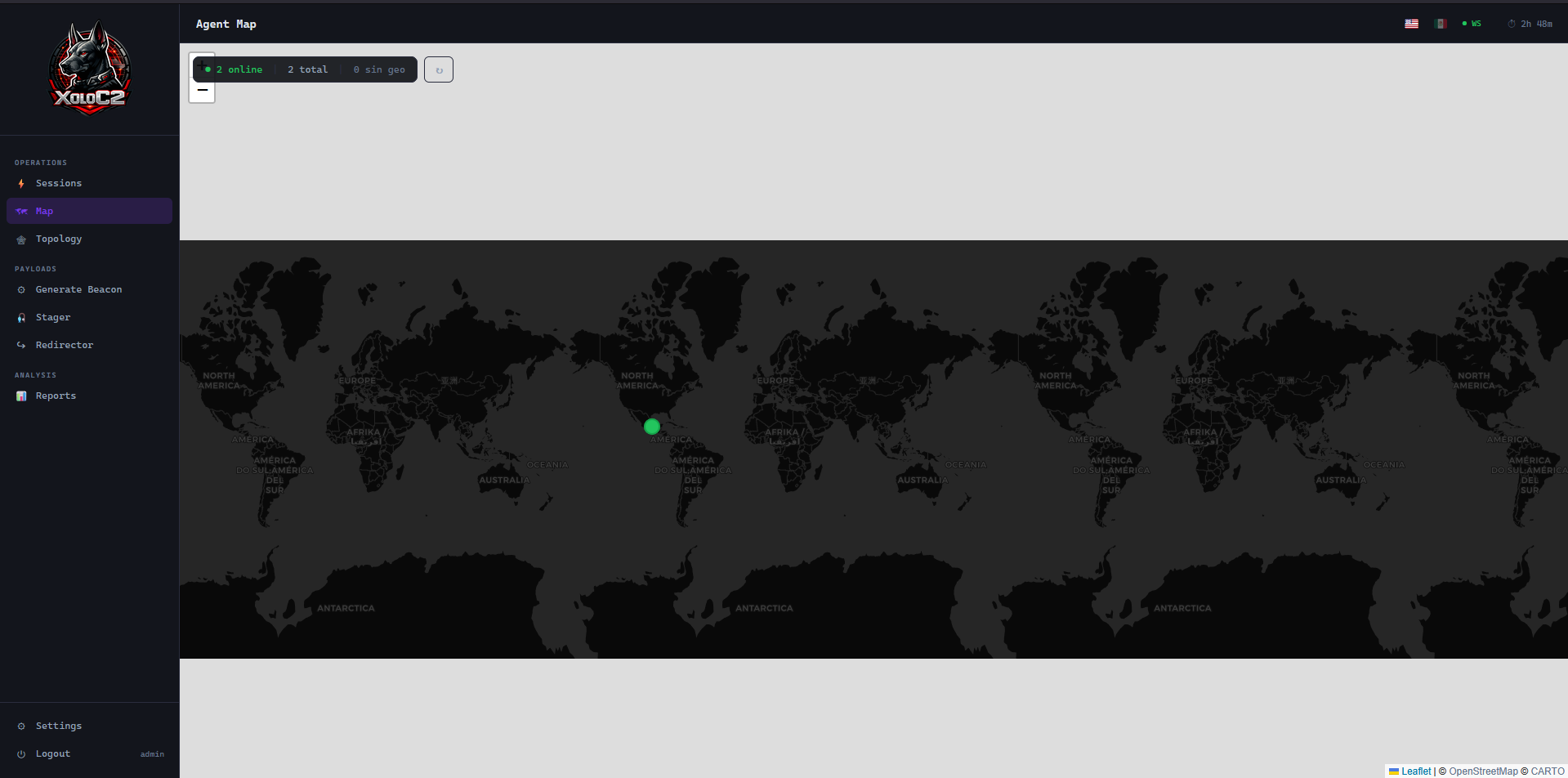
Geographic Agent Map
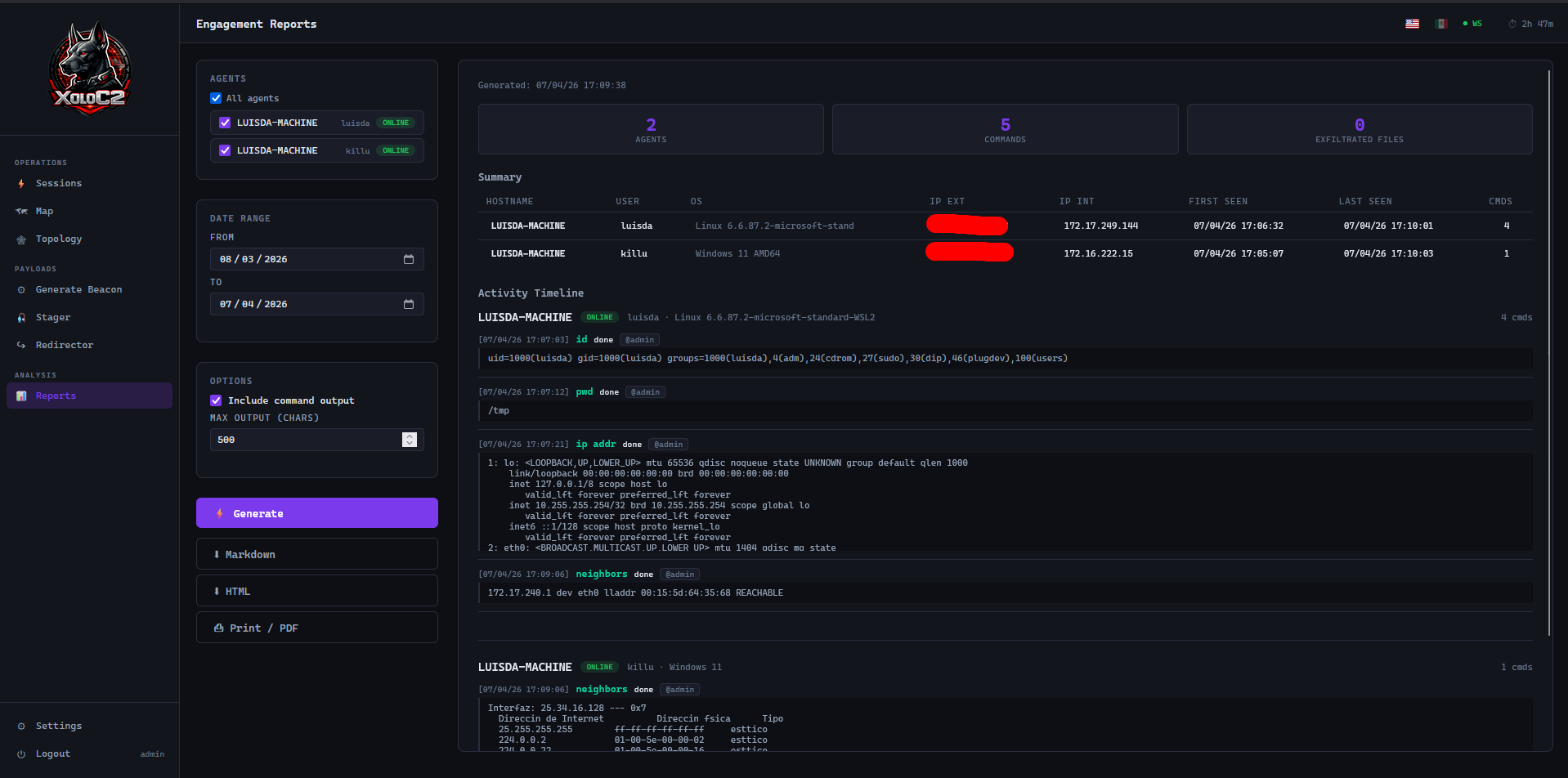
Engagement Report
Python, Java, Go, and PowerShell agents. Zero external dependencies on the target. Cross-platform Windows, Linux, and macOS.
Unique XOR key per generation, per-request XOR + nonce encryption, and server-side AES key delivery. Two beacons from the same server have different static content.
AES-256-CBC encrypted payload delivery over one-time tokens. PS IEX, HTA, VBS, curl, wget, certutil and more — all from a single stager token.
HTTP-tunnelled SOCKS5 proxy multiplexed over beacon polling. No extra tools on the target. Compatible with proxychains, Burp Suite, and any SOCKS5-aware tool.
Full interactive pseudo-terminal via xterm.js and WebSocket. CWD tracking across check-ins on both Windows and Linux.
Sandbox/VM detection, process masquerade, traffic camouflage with real browser User-Agents, kill date, heartbeat timeout, and background execution.
AMSI bypass, ETW disable, and ScriptBlock logging disable built into the PowerShell beacon. Executes in memory with no files on disk.
vis.js graph of discovered internal network. Run neighbors on any beacon to map nearby hosts and build a visual pivot map.
JWT auth, TOTP/MFA, IP whitelist, rate limiting, bcrypt passwords, audit log, agent secret rotation, and webhook notifications.
Authorized penetration testing, red team operations, and lab environments.
Resources, release history, and usage guidelines.
Clone, install, and have your C2 running in minutes.
$ git clone https://github.com/Juguitos/XoloC2.git
$ cd XoloC2
$ bash install.sh
$ ./start.sh